In an era where digital security is paramount, understanding the role of a Trusted Platform Module (TPM) in your PC is essential. This article delves into what a TPM is, its importance, and the latest developments in this technology.
Key Highlights:
- TPM stands for Trusted Platform Module, a critical security component in modern PCs.
- It improves security by securely storing cryptographic keys and ensuring system integrity.
- TPM 2.0 is the current standard, offering advanced security features.
- Essential for Windows 11 compatibility and BitLocker encryption.
- New developments in TPM technology are enhancing cybersecurity and expanding its applications.
What is a Trusted Platform Module (TPM)?
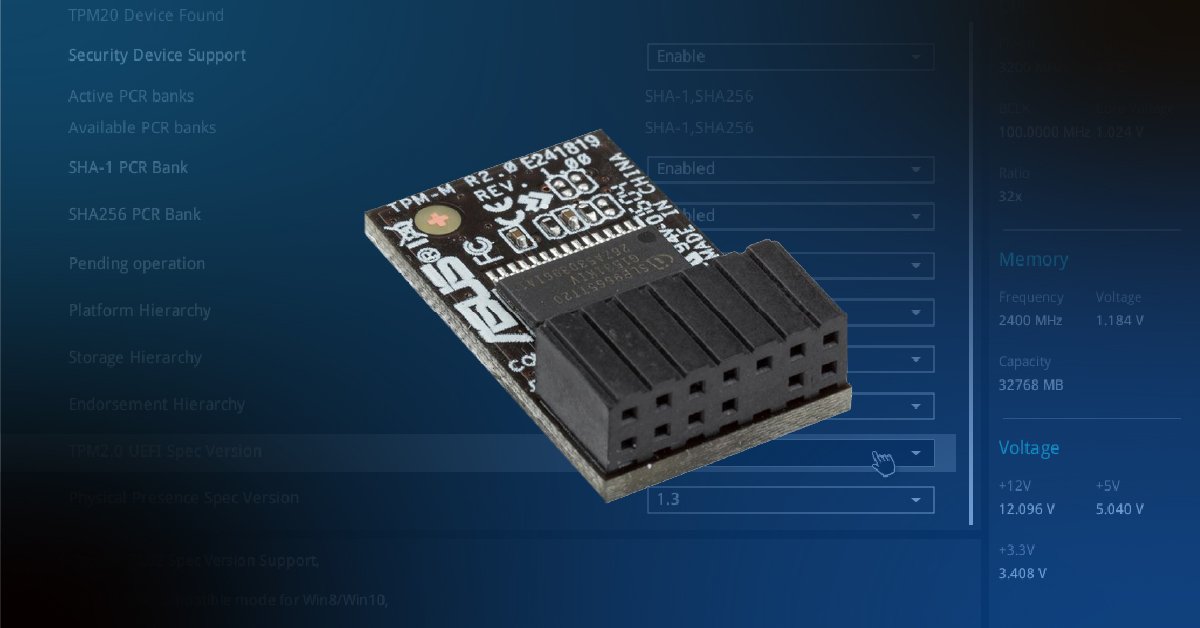
A TPM is a dedicated microcontroller designed to secure hardware through integrated cryptographic keys. Initially a separate chip, recent advancements have enabled manufacturers like Intel and AMD to integrate TPM capabilities directly into their chipsets. The TPM’s primary role is to safeguard the system by encrypting data and ensuring the integrity of the operating system and firmware.
The Evolution and Importance of TPM
Since its inception over two decades ago, TPM has evolved significantly. The current version, TPM 2.0, has become a standard in PCs since 2016. This version brought notable improvements in authorization mechanisms, cryptographic algorithms, and ease of management, making it a cornerstone of modern cybersecurity.
TPM 2.0: A Shield Against Cyber Threats
The latest TPM 2.0 Specification is a robust tool in the fight against cyber-attacks. It introduces features like the Authenticated Countdown Timer (ACT) for IoT devices, simplifies access to TPM functions with the x509Certify command, and facilitates secure data transfer to external devices. These enhancements are crucial in securing billions of IoT devices and sustaining a strong cybersecurity ecosystem.
TPM in Everyday Computing
TPM’s relevance extends to everyday users, particularly with operating systems like Windows 11, which require TPM 2.0 for installation. This requirement underscores the importance of TPM in ensuring a secure computing environment.
The Future of TPM Technology
As cyber threats evolve, so does TPM technology. The Trusted Computing Group (TCG) is actively working to expand TPM specifications to meet future security challenges. The ongoing developments promise to make TPM an even more integral component of secure computing.
The Trusted Platform Module is more than just a security feature; it’s a necessity in today’s digital world. Its role in safeguarding PCs from evolving cyber threats while enhancing system integrity cannot be overstated. As we move forward, TPM technology will continue to be a critical factor in both personal and professional computing environments.
The Journey from TPM 1.2 to TPM 2.0
The journey of TPM technology from version 1.2 to 2.0 marks a significant leap in security capabilities. While TPM 1.2 was effective for its time, TPM 2.0 introduces more robust encryption methods, enhanced authorization features, and extended functionalities for a wide range of applications. This upgrade is vital in an era where security threats are becoming increasingly complex and sophisticated.
Understanding and leveraging the power of TPM is crucial for anyone concerned with digital security and system performance. As technology advances, staying informed about developments like TPM is key to maintaining a secure and efficient computing experience.